3 Authentication
Overview
In Administration → Authentication the user authentication method to Zabbix can be changed. The available methods are internal, LDAP and HTTP authentication.
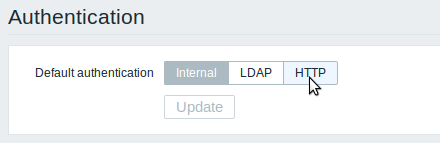
By default, internal Zabbix authentication is used. To change, click on the button with the method name and press Update.
Internal
Internal Zabbix authentication is used.
LDAP
External LDAP authentication can be used to check user names and passwords. Note that a user must exist in Zabbix as well, however its Zabbix password will not be used.
Zabbix LDAP authentication works at least with Microsoft Active Directory and OpenLDAP.
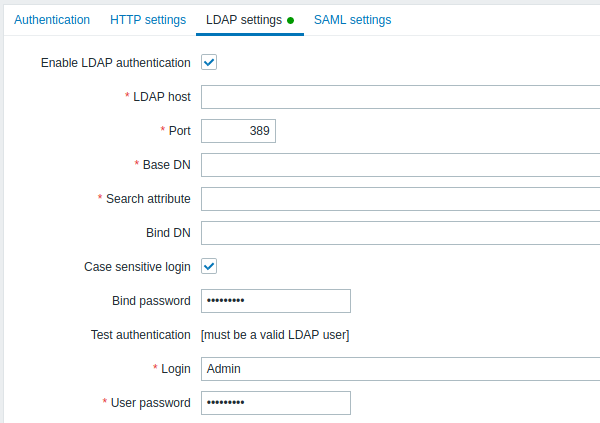
Configuration parameters:
| Parameter | Description |
|---|---|
| LDAP host | Name of LDAP server. For example: ldap://ldap.zabbix.com For secure LDAP server use ldaps protocol. ldaps://ldap.zabbix.com With OpenLDAP 2.x.x and later, a full LDAP URI of the form ldap://hostname:port or ldaps://hostname:port may be used. |
| Port | Port of LDAP server. Default is 389. For secure LDAP connection port number is normally 636. Not used when using full LDAP URIs. |
| Base DN | Base path to search accounts: ou=Users,ou=system (for OpenLDAP), DC=company,DC=com (for Microsoft Active Directory) |
| Search attribute | LDAP account attribute used for search: uid (for OpenLDAP), sAMAccountName (for Microsoft Active Directory) |
| Bind DN | LDAP account for binding and searching over the LDAP server, examples: uid=ldap_search,ou=system (for OpenLDAP), CN=ldap_search,OU=user_group,DC=company,DC=com (for Microsoft Active Directory) Required, anonymous binding is not supported. |
| Bind password | LDAP password of the account for binding and searching over the LDAP server. |
| Test authentication | Header of a section for testing |
| Login | Name of a test user (which is currently logged in the Zabbix frontend). This user name must exist in the LDAP server. Zabbix will not activate LDAP authentication if it is unable to authenticate the test user. |
| User password | LDAP password of the test user. |
In case of trouble with certificates, to make a
secure LDAP connection (ldaps) work you may need to add a
TLS_REQCERT allow line to the /etc/openldap/ldap.conf configuration
file. It may decrease the security of connection to the LDAP
catalog.
It is recommended to create a separate LDAP account
(Bind DN) to perform binding and searching over the LDAP server with
minimal privileges in the LDAP instead of using real user accounts (used
for logging in the Zabbix frontend).
Such an approach provides more security and does not require changing
the Bind password when the user changes his own password in the LDAP
server.
In the table above it's ldap_search account name.
Some user groups can still be authenticated by Zabbix. These groups must have frontend access set to Internal.
HTTP
Apache-based (HTTP) authentication can be used to check user names and passwords. Note that a user must exist in Zabbix as well, however its Zabbix password will not be used.
Be careful! Make sure that Apache authentication is configured and works properly before switching it on.
In case of Apache authentication all users (even with frontend access set to Internal) will be authenticated by Apache, not by Zabbix!
Setting up the identity provider
In order to work with Zabbix, a SAML identity provider (onelogin.com, auth0.com, okta.com, etc.) needs to be configured in the following way:
- Assertion Consumer URL should be set to
<path_to_zabbix_ui>/index_sso.php?acs - Single Logout URL should be set to
<path_to_zabbix_ui>/index_sso.php?sls
<path_to_zabbix_ui> examples: %% https://example.com/zabbix/ui,
http://another.example.com/zabbix,
<http://><any_public_ip_address>/zabbix %%
Setting up Zabbix
It is required to install php-openssl if you want to use SAML authentication in the frontend.
To use SAML authentication Zabbix should be configured in the following way:
1. Private key and certificate should be stored in the ui/conf/certs/, unless custom paths are provided in zabbix.conf.php.
By default, Zabbix will look in the following locations:
- ui/conf/certs/sp.key - SP private key file
- ui/conf/certs/sp.crt - SP cert file
- ui/conf/certs/idp.crt - IDP cert file
2. All of the most important settings can be configured in the Zabbix frontend. However, it is possible to specify additional settings in the configuration file.
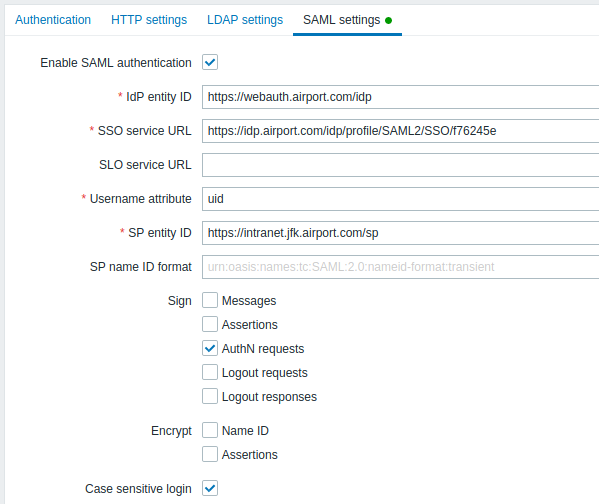
Configuration parameters, available in the Zabbix frontend:
| Parameter | Description |
|---|---|
| Enable SAML authentication | Mark the checkbox to enable SAML authentication. |
| IDP entity ID | The unique identifier of SAML identity provider. |
| SSO service URL | The URL users will be redirected to when logging in. |
| SLO Service URL | The URL users will be redirected to when logging out. If left empty, the SLO service will not be used. |
| // Username attribute// | SAML attribute to be used as a username when logging into Zabbix. List of supported values is determined by the identity provider. Examples: uid userprincipalname samaccountname username userusername <urn:oid:0.9.2342.19200300.100.1.1> <urn:oid:1.3.6.1.4.1.5923.1.1.1.13> <urn:oid:0.9.2342.19200300.100.1.44> |
| SP entity ID | The unique identifier of SAML service provider. |
| SP name ID format | Defines which name identifier format should be used. Examples: <urn:oasis:names:tc:SAML:2.0:nameid-format:persistent> <urn:oasis:names:tc:SAML:2.0:nameid-format:transient> <urn:oasis:names:tc:SAML:2.0:nameid-format:kerberos> <urn:oasis:names:tc:SAML:2.0:nameid-format:entity> |
| Sign | Mark the checkboxes to select entities for which SAML signature should be enabled: Messages Assertions AuthN requests Logout requests Logout responses |
| Encrypt | Mark the checkboxes to select entities for which SAML encryption should be enabled: Assertions Name ID |
| Case-sensitive login | Mark the checkbox to enable case-sensitive login (disabled by default) for usernames. E.g. disable case-sensitive login and log in with, for example, 'ADMIN' user even if the Zabbix user is 'Admin'. Note that with case-sensitive login disabled the login will be denied if multiple users exist in Zabbix database with similar usernames (e.g. Admin, admin). |
Advanced settings
Additional SAML parameters can be configured in the Zabbix frontend configuration file (zabbix.conf.php):
- $SSO['SP_KEY'] = '<path to the SP private key file>';
- $SSO['SP_CERT'] = '<path to the SP cert file>';
- $SSO['IDP_CERT'] = '<path to the IDP cert file>';
- $SSO['SETTINGS']
Zabbix uses OneLogin's SAML PHP Toolkit library (version 3.4.1). The structure of $SSO['SETTINGS'] section should be similar to the structure used by the library. For the description of configuration options, see official library documentation.
Only the following options can be set as part of $SSO['SETTINGS']:
- strict
- baseurl
- compress
- contactPerson
- organization
- sp (only options specified in this list)
- attributeConsumingService
- x509certNew
- idp (only options specified in this list)
- singleLogoutService (only one option)
- responseUrl
- certFingerprint
- certFingerprintAlgorithm
- x509certMulti
- singleLogoutService (only one option)
- security (only options specified in this list)
- signMetadata
- wantNameId
- requestedAuthnContext
- requestedAuthnContextComparison
- wantXMLValidation
- relaxDestinationValidation
- destinationStrictlyMatches
- rejectUnsolicitedResponsesWithInResponseTo
- signatureAlgorithm
- digestAlgorithm
- lowercaseUrlencoding
All other options will be taken from the database and cannot be overridden. The debug option will be ignored.
In addition, if Zabbix UI is behind a proxy or a load balancer, the custom use_proxy_headers option can be used:
- false (default) - ignore the option;
- true - use X-Forwarded-* HTTP headers for building the base URL.
Configuration example:
$SSO['SETTINGS'] = [
'security' => [
'signatureAlgorithm' => 'http://www.w3.org/2001/04/xmldsig-more#rsa-sha384'
'digestAlgorithm' => 'http://www.w3.org/2001/04/xmldsig-more#sha384',
// ...
],
// ...
];
