2 PostgreSQL encryption configuration
Overview
This section provides several encryption configuration examples for CentOS 8.2 and PostgreSQL 13.
Connection between Zabbix frontend and PostgreSQL cannot be encrypted (parameters in GUI are disabled), if the value of Database host field begins with a slash or the field is empty.
Pre-requisites
Install the PostgreSQL database using the official repository.
PostgreSQL is not configured to accept TLS connections out-of-the-box. Please follow instructions from PostgreSQL documentation for certificate preparation with postgresql.conf and also for user access control through ph_hba.conf.
By default, the PostgreSQL socket is bound to the localhost, for the network remote connections to allow listening on the real network interface.
PostgreSQL settings for all modes can look like this:
/var/lib/pgsql/13/data/postgresql.conf:
...
ssl = on
ssl_ca_file = 'root.crt'
ssl_cert_file = 'server.crt'
ssl_key_file = 'server.key'
ssl_ciphers = 'HIGH:MEDIUM:+3DES:!aNULL'
ssl_prefer_server_ciphers = on
ssl_min_protocol_version = 'TLSv1.3'
...For access control adjust /var/lib/pgsql/13/data/pg_hba.conf:
...
### require
hostssl all all 0.0.0.0/0 md5
### verify CA
hostssl all all 0.0.0.0/0 md5 clientcert=verify-ca
### verify full
hostssl all all 0.0.0.0/0 md5 clientcert=verify-full
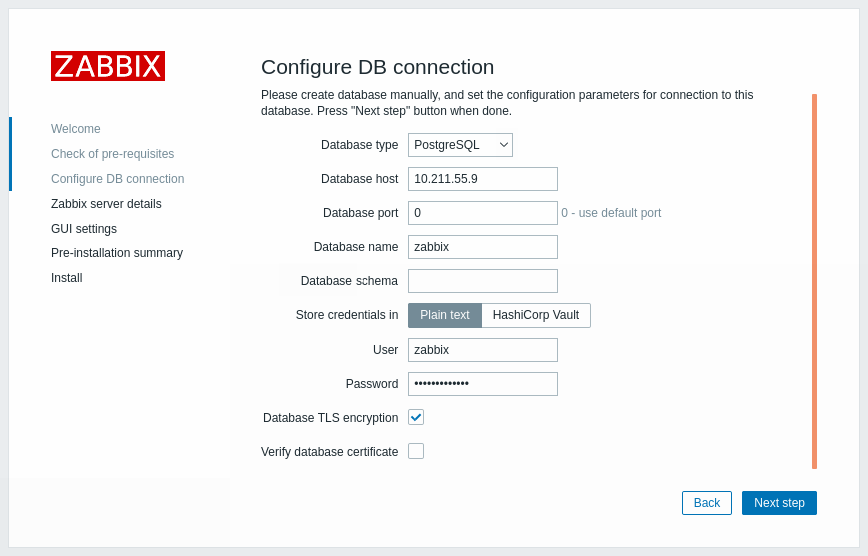
...Transport-only encryption
Frontend
To enable transport-only encryption for connections between Zabbix frontend and the database:
- Check Database TLS encryption
- Leave Verify database certificate unchecked
Server
To enable transport-only encryption for connections between server and the database, configure /etc/zabbix/zabbix_server.conf:
...
DBHost=10.211.55.9
DBName=zabbix
DBUser=zbx_srv
DBPassword=<strong_password>
DBTLSConnect=required
...Encryption with certificate authority verification
Frontend
To enable encryption with certificate authority verification for connections between Zabbix frontend and the database:
- Check Database TLS encryption and Verify database certificate
- Specify path to Database TLS CA file
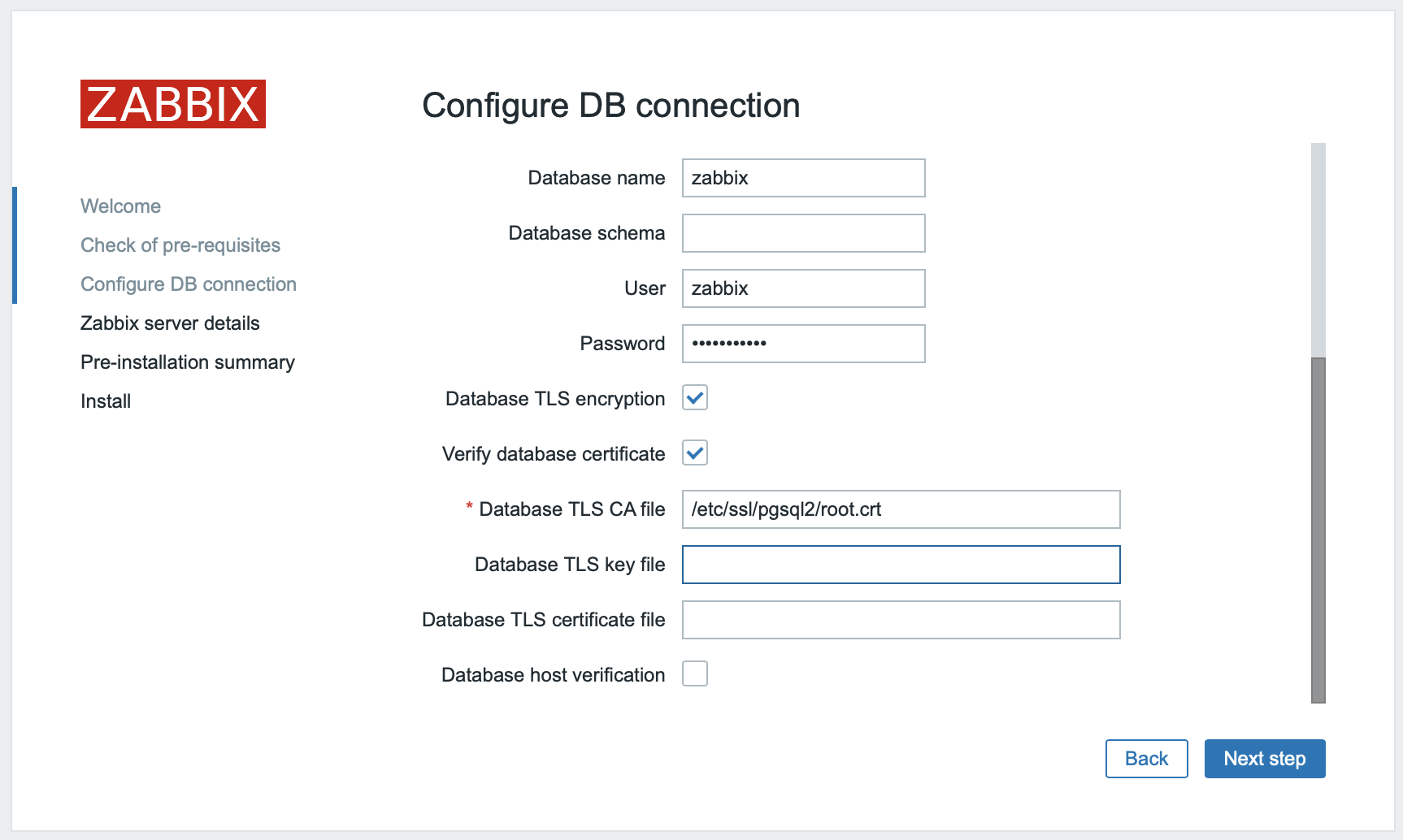
Alternatively, this can be set in /etc/zabbix/web/zabbix.conf.php:
...
$DB['ENCRYPTION'] = true;
$DB['KEY_FILE'] = '';
$DB['CERT_FILE'] = '';
$DB['CA_FILE'] = '/etc/ssl/pgsql/root.crt';
$DB['VERIFY_HOST'] = false;
$DB['CIPHER_LIST'] = '';
...Server
To enable encryption with certificate verification for connections between Zabbix server and the database, configure /etc/zabbix/zabbix_server.conf:
...
DBHost=10.211.55.9
DBName=zabbix
DBUser=zbx_srv
DBPassword=<strong_password>
DBTLSConnect=verify_ca
DBTLSCAFile=/etc/ssl/pgsql/root.crt
...Encryption with full verification
Frontend
To enable encryption with certificate and database host identity verification for connections between Zabbix frontend and the database:
- Check Database TLS encryption and Verify database certificate
- Specify path to Database TLS key file
- Specify path to Database TLS CA file
- Specify path to Database TLS certificate file
- Check Database host verification
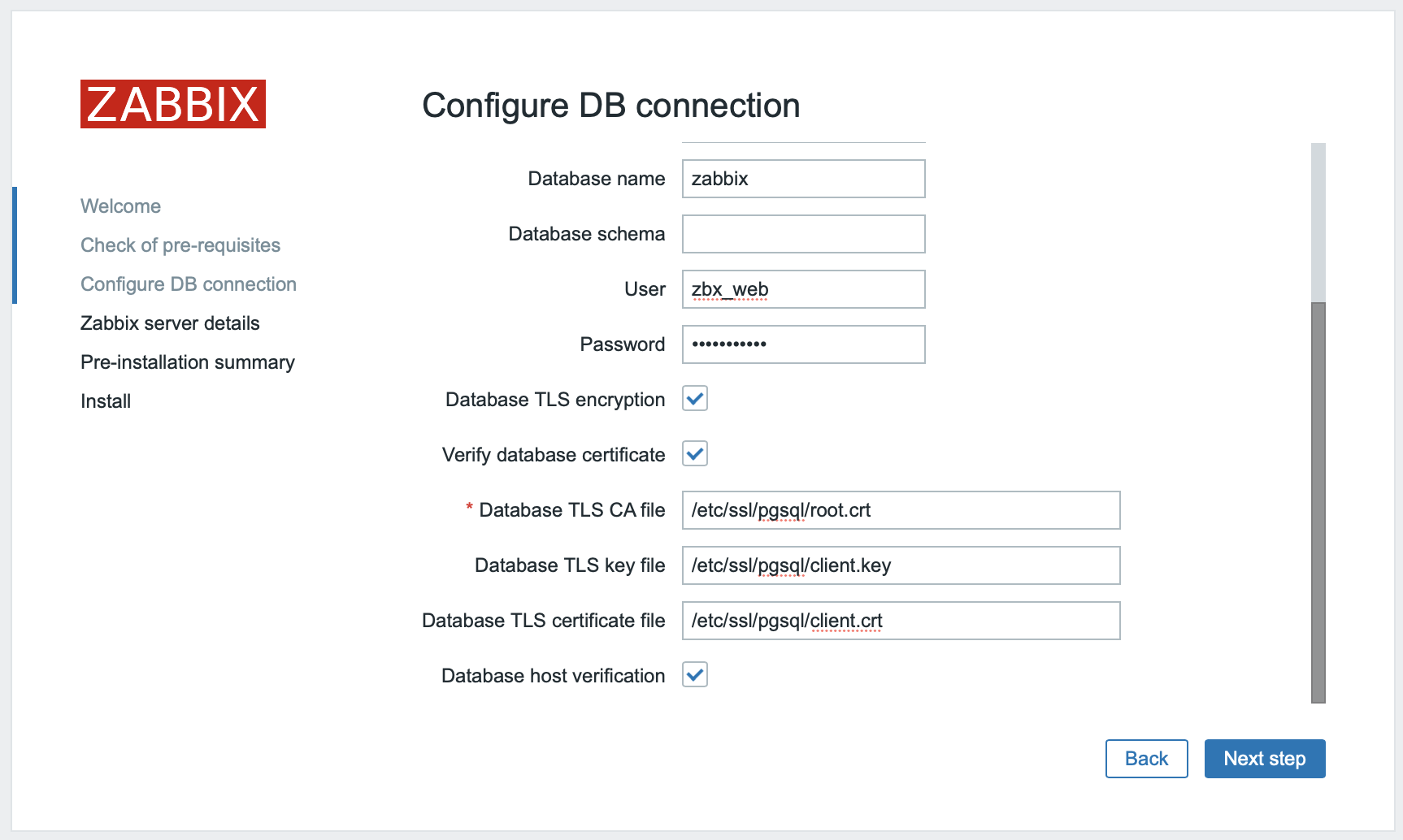
Alternatively, this can be set in /etc/zabbix/web/zabbix.conf.php:
$DB['ENCRYPTION'] = true;
$DB['KEY_FILE'] = '';
$DB['CERT_FILE'] = '';
$DB['CA_FILE'] = '/etc/ssl/pgsql/root.crt';
$DB['VERIFY_HOST'] = true;
$DB['CIPHER_LIST'] = '';
...Server
To enable encryption with certificate and database host identity verification for connections between Zabbix server and the database, configure /etc/zabbix/zabbix_server.conf:
...
DBHost=10.211.55.9
DBName=zabbix
DBUser=zbx_srv
DBPassword=<strong_password>
DBTLSConnect=verify_full
DBTLSCAFile=/etc/ssl/pgsql/root.crt
DBTLSCertFile=/etc/ssl/pgsql/client.crt
DBTLSKeyFile=/etc/ssl/pgsql/client.key
...
